LinkedIn’s enforcement is faster, smarter, and harder to reverse than ever. The tool you choose is now the single biggest variable in whether your account stays safe.
If you’ve been automating LinkedIn outreach for a while, you’ve probably noticed the landscape shifting under your feet. Connection request limits are tighter.
Restrictions happen faster. And recovery? It’s become a slow, painful process with no guarantee your account comes back to full health.
LinkedIn’s detection systems have evolved significantly. What worked in 2023 barely survived 2024, and by 2025, the platform rolled out its Zero-Trust security model, an architecture designed to verify every session, every action, every device. In 2026, the enforcement isn’t just reactive. It’s predictive.
This article isn’t about which tool has better features, more integrations, or a sleeker dashboard. It’s about something more fundamental: which architecture keeps your LinkedIn account alive?
Here’s what most people don’t realise: the majority of LinkedIn automation tool warnings, the ones that lead to temporary restrictions, connection limits, and outright bans, stem from one specific category of tool. And by the end of this article, you’ll understand exactly why.
How Chrome Extensions Actually Work (And What LinkedIn Sees)
Let’s get technical for a moment, in plain language.
When you install a LinkedIn automation Chrome extension, it injects code directly into your LinkedIn browser tab. It manipulates the DOM (the underlying structure of the webpage), clicks buttons, scrolls through profiles, and sends messages by mimicking your actions inside the browser.
Here’s the critical part: every action runs client-side. That means the extension operates from your IP address, your browser fingerprint, and your session cookies. LinkedIn’s front-end detection scripts can see the extension’s DOM manipulation in real-time.
Common Misconception
Can LinkedIn detect “human-like” randomised delays?
Yes. Pattern analysis goes far beyond timing intervals. LinkedIn’s detection systems analyse mouse movement trajectories, scroll behaviour, click coordinates, and action sequences. An extension that adds random 3-7 second delays between actions is still exhibiting machine patterns in every other dimension. The delays are a thin disguise on a fundamentally detectable behaviour.
This is why Chrome extensions trigger the most LinkedIn automation tool warnings. The extension is literally sitting inside LinkedIn’s front door, manipulating the page while LinkedIn watches.
The Multi-Account Problem
It gets worse if you manage multiple LinkedIn accounts. Running several accounts through extensions on the same browser and IP address is one of the biggest red flags in LinkedIn’s detection system. Same browser fingerprint, same IP, different accounts, same extension behaviour patterns. To LinkedIn’s systems, this is an unmistakable signal of automation abuse.
How Cloud-Based Tools Work (And Why the Architecture Is Fundamentally Different)
Cloud-based LinkedIn automation tools take an entirely different approach. Instead of injecting code into your browser, they operate from a remote server. Your browser is never involved in the automation process.
Here’s what that means in practice:
- Dedicated IP addresses or rotating residential proxies are assigned per account, so each account appears to be logging in from its own location on its own device
- Session management happens server-side, completely outside LinkedIn’s front-end detection layer
- No code injection, no DOM manipulation, and no browser fingerprint inconsistencies
- No dependency on your computer being on, automation runs 24/7 in the background
This architecture aligns with LinkedIn’s 2026 Zero-Trust security model. To LinkedIn, a cloud-based session looks like a user logging in from another device, which is perfectly normal behaviour in a world where people access LinkedIn from phones, tablets, laptops, and desktops throughout the day.
Key Takeaway
Cloud-based LinkedIn automation is considered the safer architecture because it operates at the infrastructure level, not the browser level. There’s nothing for LinkedIn’s front-end scripts to detect because the automation never touches the front end.
The 2026 Risk Matrix: Side-by-Side Comparison
Here’s how the two architectures compare across every safety dimension that matters:
| Risk Factor | Chrome Extension | Cloud-Based Tool |
|---|---|---|
| DOM Injection Detection | High risk — injects directly into LinkedIn’s page | No risk — no browser interaction |
| Browser Fingerprint | Exposed — uses your actual fingerprint | Isolated — dedicated cloud session |
| IP Address Exposure | Your personal/office IP is visible | Residential or dedicated IPs per account |
| Multi-Account Safety | Major red flag — same browser, same IP | Fully isolated environments per account |
| Behaviour Pattern Analysis | Detectable — machine patterns visible client-side | Minimal exposure — actions happen server-side |
| Warm-Up Capability | Requires you to be online and active | Runs automatically in the background |
| Zero-Trust Compatibility | Conflicts with session verification | Appears as a legitimate additional device |
| Restriction Diagnosis | Difficult — tangled with personal activity | Clear logs, dashboards, and support |
The “Warm-Up” Factor: Why Cloud Tools Have a Structural Advantage
Warm-up is not optional in 2026. LinkedIn’s algorithm flags accounts that go from dormant to high-volume overnight. If your account has been quiet for weeks and suddenly sends 50 connection requests in a day, that’s a bright red signal, regardless of which tool you use.
Here’s how you can warm up a new LinkedIn account for automation:
Start with low-volume, organic-looking activity: profile views, content engagement, follows, and a handful of connection requests per day. Gradually increase volume over 2-3 weeks until you reach your target activity level. This teaches LinkedIn’s algorithm that your account is active and growing naturally.
Here’s where the architectural difference becomes practical:
Chrome extensions require you to be online, with your browser open and the extension running, for warm-up actions to execute. If you close your laptop, the warm-up stops. If you go on holiday, your account goes dormant again.
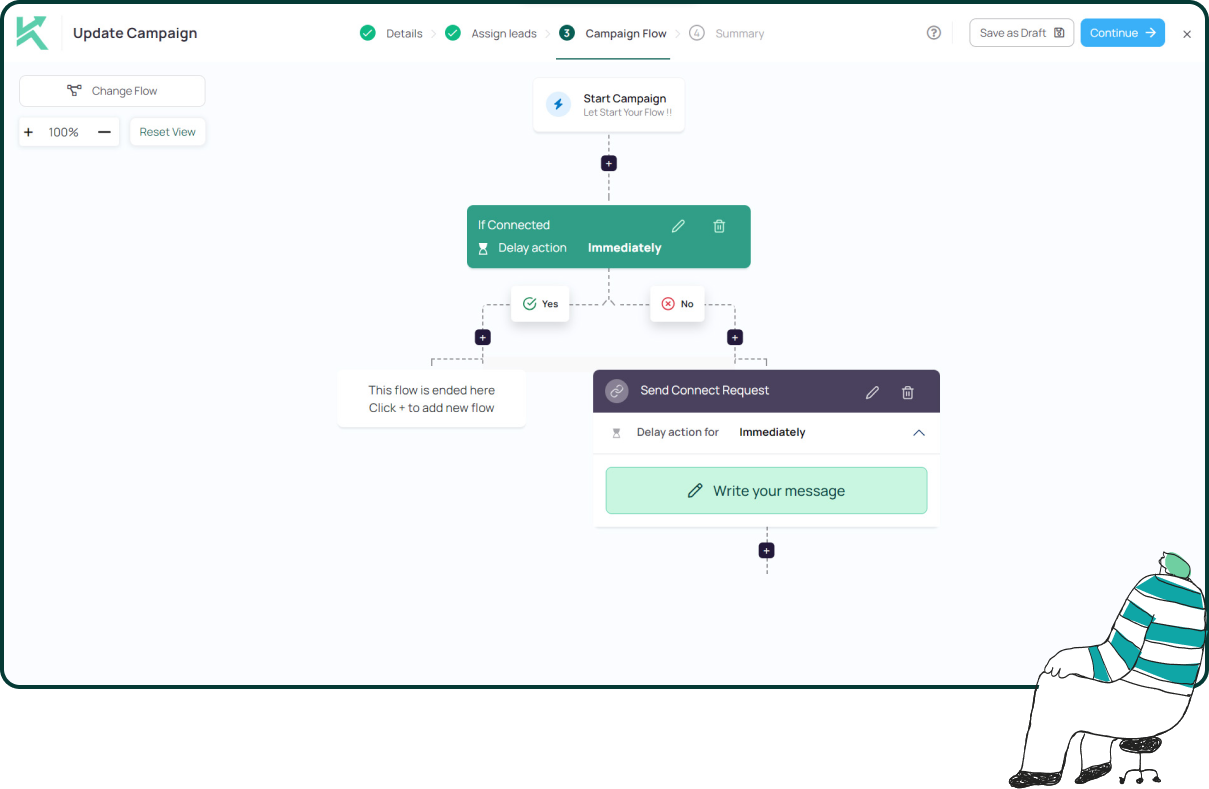
Cloud-based tools like Konnector.AI run warm-up micro-actions automatically in the background: profile views, follows, content engagement, all simulating a gradual, organic ramp-up over days and weeks without any manual effort from you. Your account stays consistently active whether you’re at your desk or not.
What Happens When Things Go Wrong: Restriction and Recovery
No system is bulletproof. Even with the best tool and the most conservative settings, restrictions can happen. What matters is how quickly you can diagnose the problem and recover.
Now if you’re wondering – what you should do if your LinkedIn account gets restricted, here’s a simple guide:
Stop all automation immediately. Wait 24-48 hours before taking any action. Review your recent activity for anything that could have triggered the restriction: sudden volume spikes, aggressive sequences, or high spam report rates. If using a cloud-based tool, check the activity logs to identify the exact trigger. Gradually resume activity at a much lower volume.
Chrome extension restrictions are harder to diagnose because the cause is tangled with your personal browser activity. Was it the extension? Was it a manual action you took? Was it a browser update that changed a fingerprint parameter? The debugging surface area is enormous.
Cloud-based tools typically offer detailed activity logs, dashboards, and dedicated support to identify exactly what triggered a restriction. The automation is isolated from your personal activity, so the cause-and-effect relationship is much clearer.
Read more—-> What should you do if your LinkedIn account gets restricted?
How to Avoid “LinkedIn Jail”
- Respect weekly connection request limits. LinkedIn’s threshold sits around 100-150 per week for healthy, established accounts. New or recently restricted accounts should stay well below this.
- Never exceed daily message thresholds. Staying under 50-70 messages per day is a widely accepted safe range.
- Avoid aggressive sequences on cold prospects. Multiple follow-ups to someone who hasn’t responded signals spam behaviour to LinkedIn’s systems.
- Monitor your acceptance rate. If fewer than 20-30% of your connection requests are being accepted, your targeting needs work, not your volume.
Does Sales Navigator Change the Safety Equation?
This is one of the most common questions in LinkedIn automation, and the answer is frequently misunderstood.
Does using Sales Navigator make my automation safer? No. Sales Navigator is a data and filtering layer, not a protection layer. It does not shield your account from detection or make automation inherently less risky.
However, Sales Navigator does improve safety indirectly. Better targeting means fewer irrelevant messages, which means fewer “report spam” clicks from recipients, which means a healthier sender reputation. The safety improvement comes from better targeting accuracy, not from the tool itself.
This is why the combination matters. Cloud-based tools that integrate with Sales Navigator, like Konnector.AI, pair better targeting with safer infrastructure. You get the precision of Sales Navigator’s filters with the architectural safety of cloud-based execution. Sales Navigator automation tools work best when paired with cloud architecture, not extensions.
Read more—-> Use LinkedIn Sales Navigator for Free With Konnector.AI extension
The VPN and Proxy Question
Can LinkedIn detect if I’m using a VPN or Proxy?
Yes. LinkedIn can detect most commercial VPN and datacentre proxy IPs. These IP ranges are well-known and frequently flagged by LinkedIn’s security systems.
Here’s why a VPN doesn’t solve the Chrome extension problem: even with a VPN masking your IP, the extension is still injecting code into the DOM. The IP layer is only one detection vector. LinkedIn’s front-end scripts can still see the DOM manipulation, the machine-like interaction patterns, and the browser fingerprint inconsistencies.
Cloud-based tools use residential or dedicated IPs that are significantly harder to flag because they look like normal consumer internet connections. But more importantly, they eliminate the other detection vectors entirely: no DOM injection, no browser fingerprint exposure, no client-side pattern analysis.
The real point: a VPN is a band-aid on the wrong problem. The architecture of the tool matters more than the IP layer you put in front of it.
Why Konnector.AI Built Cloud-First (Not as an Afterthought)
Konnector.AI was designed from day one as a cloud-based LinkedIn automation platform, not a Chrome extension that bolted on a cloud option later. This distinction matters because the entire product architecture, from session management to IP handling to warm-up logic, was built around cloud-native safety principles.
About the Konnector Chrome Extension
Konnector does have a Chrome extension, but it works fundamentally differently from automation extensions. The Konnector extension does not perform browser automation. It does not operate from your IP address, your browser fingerprint, or your session cookies. It exists purely for convenience: attaching your LinkedIn account and gathering lead lists easily. Even when you use Konnector’s Chrome extension, all LinkedIn activities happen on a dedicated cloud session. No actions happen on your browser. No HTML injections. Your IP is never used. Your browser is never used.
Konnector.AI Cloud-First Safety Features
Every feature built around account protection, not bolted on later.
The key difference: when LinkedIn’s systems look at a Konnector.AI session, all they see is a user logging in from another device. There’s no DOM manipulation to detect, no extension code to flag, and no browser fingerprint anomalies to trigger an alert. It’s structurally invisible to the detection vectors that catch Chrome extensions.
The Verdict
Chrome extensions are not inherently “evil.” Many were built with good intentions and offered useful features. But their architecture, injecting code into LinkedIn’s browser tab and operating from your personal session, exposes you to detection risks that cloud tools simply don’t have.
In 2026, with LinkedIn’s Zero-Trust updates and smarter detection systems, the safest LinkedIn automation tool is one that never touches your browser.
Cloud-based is the safer architecture. Period.
And among cloud-based tools, the ones that were built cloud-first, like Konnector.AI, rather than those that retrofitted a cloud option onto their extension later. Get the best of both and learn how to automate your LinkedIn outreach safely by booking a demo with us!
11x Your LinkedIn Outreach With
Automation and Gen AI
Harness the power of LinkedIn Automation and Gen AI to amplify your reach like never before. Engage thousands of leads weekly with AI-driven comments and targeted campaigns—all from one lead-gen powerhouse platform.
Frequently Asked Questions
Yes. Cloud-based tools are structurally safer because they run automation from remote servers instead of your browser. This removes major detection signals such as DOM injection, browser fingerprint exposure, and client-side behaviour tracking that extensions cannot hide.
Yes. LinkedIn can detect browser-level automation patterns including DOM manipulation, click sequences, scroll behaviour, and browser fingerprint anomalies. Extensions operate inside your session, making them visible to LinkedIn’s front-end monitoring systems.
Restrictions usually happen due to behavioural signals, not the tool itself. Sudden activity spikes, aggressive outreach volume, low acceptance rates, repetitive messaging patterns, or multiple accounts using the same browser/IP can trigger LinkedIn’s risk systems.
LinkedIn’s Zero-Trust system verifies every login session, device, and activity instead of assuming trust. This means automation tools that mimic browser actions are easier to flag, while server-side automation that appears as a normal device login is less suspicious.
No. A VPN only masks your IP address. It does not hide browser automation signals such as DOM injections, click behaviour patterns, or fingerprint inconsistencies. Detection systems evaluate multiple factors, not just IP location.
Start with low-volume actions such as profile views, likes, follows, and a few connection requests daily. Increase activity gradually over 2–3 weeks. This builds behavioural trust signals that show LinkedIn your account is active and growing naturally.
No. Sales Navigator improves targeting accuracy but does not reduce automation detection risk. Safety comes from behaviour quality and tool architecture, not from using Sales Navigator itself.
The safest setup combines
• cloud-based execution
• dedicated session environments
• smart activity limits
• gradual warm-up
• high targeting accuracy
This combination minimizes detection signals while maintaining natural-looking behaviour.
Yes. Running multiple accounts from the same browser or IP is a major risk signal. LinkedIn’s systems can detect identical device fingerprints and activity patterns across accounts, which often leads to restrictions.
Stop automation right away, wait 24–48 hours, review recent activity for triggers, reduce activity volume significantly, and resume gradually. Acting slowly signals normal user behaviour and improves recovery chances.








