If you’re running LinkedIn outreach at scale, you’ve probably asked yourself: can LinkedIn actually tell if I’m using a VPN or proxy? The short answer is yes — and more often than you might think. In this post, we’ll break down exactly how LinkedIn detects VPNs and proxies, why it matters for your outreach campaigns, and what you should do instead to keep your account safe and your outreach effective.
Can LinkedIn Detects VPNs and Proxies?
LinkedIn has invested heavily in fraud and bot detection. So, yes it can. Here’s how they identify unusual connection behavior:
1. IP Reputation Databases
LinkedIn cross-references your IP address against known VPN and datacenter IP ranges. Services like MaxMind, IPQualityScore, and others maintain constantly updated lists of IPs belonging to VPN providers, data centers, and proxy services. If your IP shows up in these databases, LinkedIn flags it immediately — even before you do anything suspicious.
2. Datacenter vs. Residential IP Detection
Most VPNs and proxies route your traffic through datacenter IPs (servers in AWS, DigitalOcean, etc.). LinkedIn can tell the difference between a datacenter IP and a genuine residential IP. A real user sitting at home or in an office has a residential ISP address. If you suddenly connect from a datacenter IP in Frankfurt when your account is usually active from Mumbai, that’s a red flag.
3. Geolocation Inconsistencies
LinkedIn tracks the geolocation history of your account. If your account normally logs in from one city and suddenly shows activity from a different country — especially within hours of each other — LinkedIn’s systems flag this as suspicious. This is one of the most common triggers for account restrictions during LinkedIn outreach campaigns.
4. Browser Fingerprinting
Even with a VPN active, your browser leaks a surprising amount of data: screen resolution, installed fonts, timezone, language settings, WebGL renderer, and more. If your browser fingerprint says you’re in India but your IP says you’re in the Netherlands, LinkedIn’s systems notice the mismatch.
5. DNS and WebRTC Leaks
Many VPNs suffer from DNS or WebRTC leaks that expose your real IP address even while the VPN is connected. LinkedIn’s client-side scripts can detect these leaks and identify your true location, making the VPN essentially useless from a detection standpoint.
6. Behavioral Pattern Analysis
Beyond IP detection, LinkedIn monitors behavioral signals: how fast you’re sending connection requests, how many profile views you’re making per hour, message response patterns, and session durations. A VPN doesn’t mask any of this. If your outreach activity looks automated, LinkedIn will restrict you regardless of what IP you’re coming from.
What Happens When LinkedIn Flags Your Account
When LinkedIn detects suspicious activity — whether from a VPN, proxy, or unusual behavior — the consequences escalate quickly:
- CAPTCHA challenges — You’ll be asked to verify you’re human more frequently.
- Login verification — LinkedIn may ask you to verify via email or phone before proceeding.
- Temporary restrictions — Your ability to send connection requests or messages gets throttled.
- Account warning — LinkedIn sends a formal notice that your account has violated their User Agreement.
- Permanent account ban — Repeated violations can result in your account being permanently suspended, killing all your LinkedIn outreach efforts.
For businesses that rely on LinkedIn outreach as a core lead generation channel, a banned account isn’t just an inconvenience — it can mean losing years of built-up connections and pipeline.
Why People Use VPNs for LinkedIn Outreach (and Why It Usually Backfires)
The most common reasons people turn to VPNs for LinkedIn outreach include:
- Running multiple LinkedIn accounts from the same machine
- Trying to bypass LinkedIn’s weekly connection request limits
- Accessing LinkedIn from restricted regions
- Attempting to hide automation tool usage from LinkedIn’s servers
The problem is that VPNs address the wrong layer of the problem. LinkedIn’s detection isn’t purely IP-based — it’s multi-layered. A VPN might mask your IP, but it does nothing to hide your browser fingerprint, your behavioral patterns, or the automation signals your outreach tool generates. You end up with a false sense of security while the real risk factors remain completely exposed.
Read more—-> The Ultimate Guide: Scrape LinkedIn in 2026 with Konnector.AI
The Right Way to Do LinkedIn Outreach Without Getting Banned
Instead of relying on VPNs and proxies, here’s what actually protects your account and keeps your LinkedIn outreach running smoothly:
Stay Within LinkedIn’s Limits
LinkedIn allows approximately 100–200 connection requests per week for standard accounts. Pushing past this limit is one of the fastest ways to trigger a restriction. A well-structured outreach strategy works within these limits and relies on quality targeting rather than volume.
Use Dedicated Residential Proxies (If Needed for Multiple Accounts)
If you absolutely need to manage multiple LinkedIn accounts, dedicated residential proxies — not shared datacenter proxies — are far less likely to be flagged. Each account should have a consistent, unique residential IP assigned to it, and you should never share IPs across accounts.
Warm Up New Accounts Properly
New LinkedIn accounts that jump straight into heavy outreach get flagged almost immediately. A proper warm-up period — gradually increasing activity over 4–6 weeks — looks far more natural to LinkedIn’s systems.
Humanize Your Outreach Messages
Mass-copied, templated messages are a behavioral signal LinkedIn’s spam detection picks up on. Personalized outreach — even lightly personalized — performs better both algorithmically and in terms of actual response rates. Your LinkedIn outreach should feel like a real conversation, not a broadcast.
Use a Compliant LinkedIn Outreach Tool
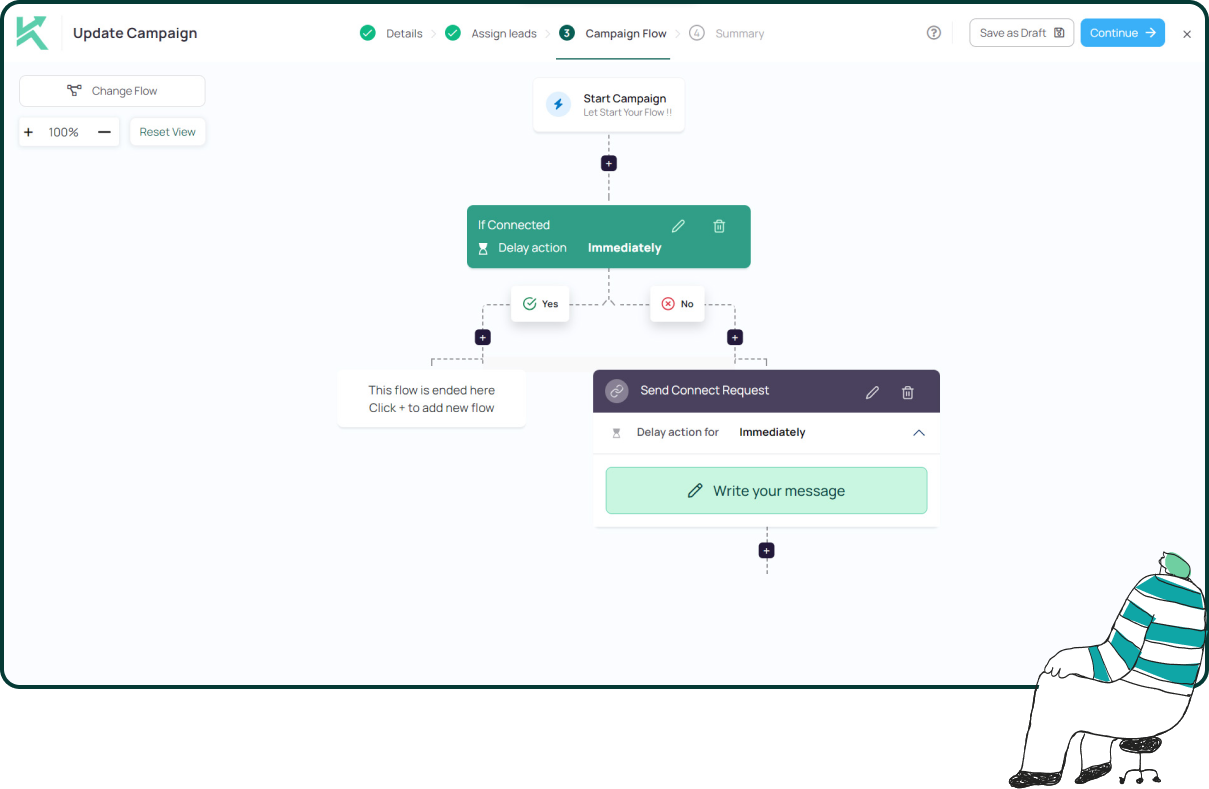
This is where tools like Konnector.ai make a real difference. Rather than using risky workarounds like VPNs or proxies, Konnector.ai is built to work within LinkedIn’s boundaries — respecting rate limits, mimicking natural human behavior, and keeping your account safe while still delivering results at scale.
Read more—-> How to get clients with LinkedIn Automation?
Konnector.ai: LinkedIn Outreach Done Right
At Konnector.ai, we’ve built our platform specifically around safe, effective LinkedIn outreach. We don’t recommend using VPNs or proxies with our tool — and here’s why:
Our system already handles the complexity of safe outreach for you. Smart throttling, human-like delays, personalized message sequences, and activity limits are all built in. You don’t need to layer risky VPN workarounds on top of a tool that’s already designed to keep you compliant.
The goal of LinkedIn outreach isn’t to game the platform — it’s to build genuine relationships with your ideal prospects at scale. That requires working with LinkedIn, not against it.
Read more—-> Is LinkedIn Automation Safe in 2026?
Final Thoughts
Yes, LinkedIn can detect VPNs and proxies — and with increasing accuracy. Between IP reputation databases, browser fingerprinting, geolocation analysis, and behavioral monitoring, the platform has multiple overlapping systems designed to catch exactly the kind of workarounds most people try.
For anyone serious about LinkedIn outreach as a lead generation channel, the answer isn’t to hide better — it’s to build a compliant, sustainable outreach strategy from the ground up. Protect your account, respect the platform’s limits, and use the right tools for the job.
Ready to run LinkedIn outreach that actually scales without putting your account at risk? Try Konnector.ai today.
11x Your LinkedIn Outreach With
Automation and Gen AI
Harness the power of LinkedIn Automation and Gen AI to amplify your reach like never before. Engage thousands of leads weekly with AI-driven comments and targeted campaigns—all from one lead-gen powerhouse platform.
Frequently Asked Questions
Yes. LinkedIn cross-references your IP address with known VPN and datacenter IP databases. If your IP matches flagged ranges, your account may be marked for review — even before unusual behavior occurs.
No. VPNs only mask IP addresses. LinkedIn also analyzes browser fingerprinting, behavioral activity, geolocation patterns, and session data. A VPN does not protect you from these signals.
Residential proxies are less likely to be flagged because they mimic real ISP traffic. However, misuse, aggressive outreach behavior, or inconsistent login patterns can still trigger restrictions.
Because most proxy IPs belong to data centers. LinkedIn treats these as high-risk traffic sources commonly associated with automation and spam behavior.
Frequent CAPTCHA prompts, login verification requests, throttled connection limits, and warning notifications are early red flags.
Yes. LinkedIn monitors behavioral signals such as rapid connection requests, identical messaging patterns, unusual session timing, and activity spikes.
Typically 100–200 per week for standard accounts. The safest strategy focuses on targeting quality prospects rather than maximizing volume.
Gradually increase activity over 4–6 weeks. Start with profile optimization, organic engagement, and low-volume connection requests before scaling outreach.
Yes — if done correctly. Cloud-based, compliance-focused tools like Konnector.ai are designed to respect LinkedIn limits, mimic natural behavior, and reduce risk
Use a compliant LinkedIn automation platform like Konnector.ai that includes smart throttling, human-like delays, CRM integration, and behavioral pattern optimization instead of risky VPN workarounds.









