Quick answer: LinkedIn detects headless browsers through a layered system that checks TLS handshake fingerprints, JavaScript environment properties like navigator.webdriver, DOM injection signatures from browser extensions, missing browser attributes, IP geolocation, and behavioural patterns — all simultaneously. No single signal triggers a flag; LinkedIn evaluates the whole stack. Understanding each layer is essential for anyone running LinkedIn automation safely in 2026.
What Is a Headless Browser and Why Does LinkedIn Target It?
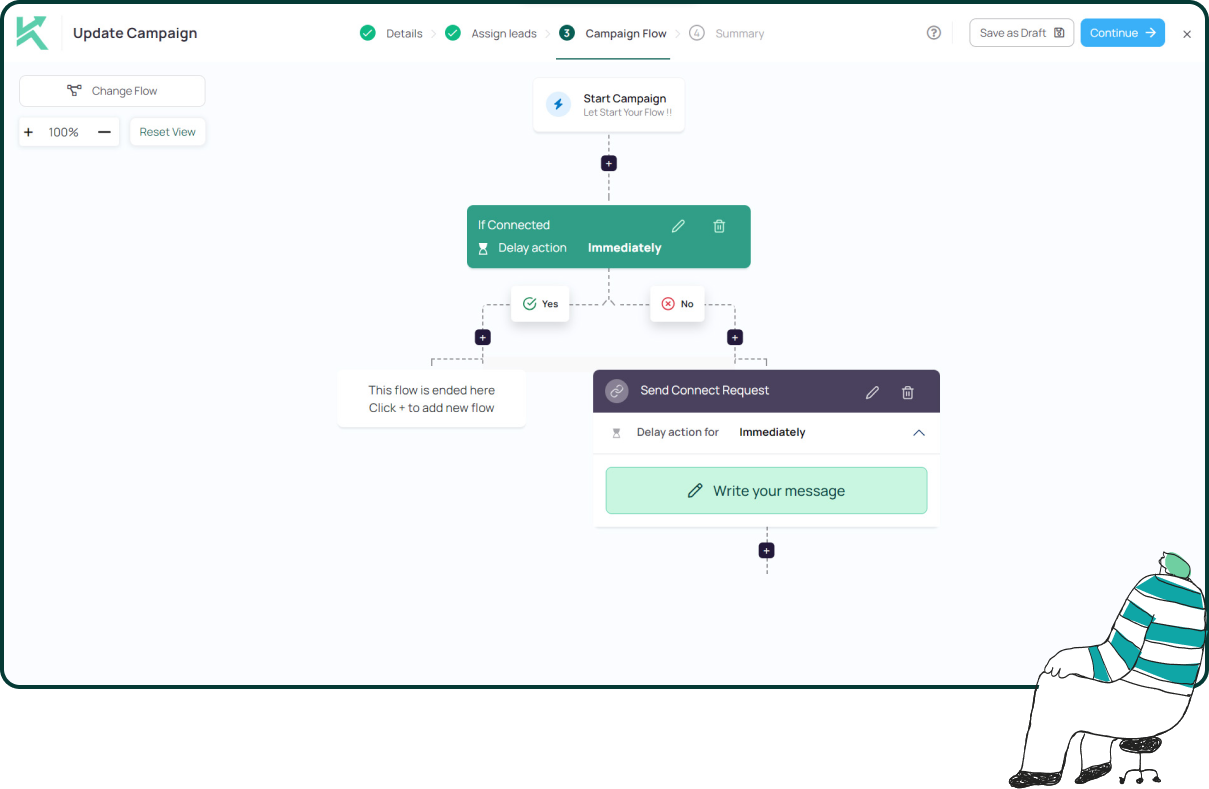
A headless browser is a web browser running without a graphical user interface, controlled entirely by code. Tools like Puppeteer, Playwright, and Selenium use headless Chrome to automate LinkedIn actions — visiting profiles, sending connection requests, and firing messages — at machine speed.
LinkedIn explicitly prohibits headless browsers in its User Agreement. The reason is straightforward: headless execution is the technical foundation of every bot, scraper, and spam tool on the platform. In 2026, LinkedIn’s detection infrastructure operates at multiple layers simultaneously, making naive headless implementations detectable within minutes.
The Six Detection Layers LinkedIn Uses in 2026
1. TLS Fingerprinting
This is the most underestimated detection layer. Every browser leaves a TLS fingerprint — a signature of the cipher suites, extensions, and elliptic curves it proposes during the SSL/TLS handshake when establishing a secure connection. Real Chrome produces a specific, well-documented TLS signature (JA3/JA4 hash). Headless Chrome and tools built on Node.js default to different underlying TLS library configurations, producing a mismatched handshake.
Critically, LinkedIn can inspect this fingerprint before any page content loads. A request claiming to be Chrome but carrying a non-Chrome TLS profile is flagged at the network layer, before any JavaScript runs. This is why simply spoofing a Chrome user-agent string is insufficient protection.
2. The navigator.webdriver Property
Any browser controlled by Puppeteer, Playwright, or Selenium automatically sets navigator.webdriver = true in the JavaScript environment. LinkedIn’s page scripts check for this property on load. It is the fastest and most direct confirmation that a session is automated. Stealth plugins can suppress this property, but doing so creates other inconsistencies that compound the fingerprint mismatch.
3. Missing Browser Environment Properties
A genuine Chrome browser running on a real device has a populated set of properties: browser plugins, a real GPU-rendered WebGL renderer, standard font arrays, functional window.chrome and window.chrome.runtime objects, and realistic screen dimensions. Headless Chrome, by default, returns empty plugin arrays, software WebGL renderers, and absent or broken window.chrome objects. LinkedIn’s JavaScript checks score these signals against expected values for a genuine Chrome session and build a confidence rating for whether the session is human.
4. DOM Injection Detection
Browser extension-based LinkedIn automation tools inject foreign code — classes, IDs, and event listeners — directly into LinkedIn’s page structure (the Document Object Model). LinkedIn’s scripts scan their own page for foreign elements. Any extension adding “Auto-Connect” buttons or modifying page behaviour leaves a detectable trace in the DOM that LinkedIn’s security layer identifies in real time.
This is why LinkedIn’s 2026 algorithm uses DOM Injection detection for browser extensions as one of its three primary detection methods, alongside IP tracking and behavioural analysis. Book a Konnector.ai demo to see how our hybrid execution model avoids all three.
5. IP Geolocation and “Impossible Travel”
If your personal LinkedIn account normally logs in from Dublin at 9 AM, and a cloud-based automation tool simultaneously logs in from a Frankfurt data-centre server at 9:01 AM, LinkedIn flags this as geographically impossible for a single human user. LinkedIn maintains an extensive IP reputation database. Data-centre IPs from AWS, Azure, and Google Cloud are pre-classified as high-risk and often blocked at the authentication layer before any session is established. Residential IPs matched to your account’s normal location are the 2026 baseline requirement for cloud-based tools.
6. Behavioural Analysis
Even if all fingerprint signals are clean, behavioural patterns remain detectable. LinkedIn analyses typing cadence (characters entered in 0.01 seconds is not human), scroll patterns, mouse movement trajectories, session duration, action density (50 actions in 3 minutes), and consistency of timing across sessions. A headless tool that executes actions at machine precision — every click spaced exactly 30 seconds apart — produces a statistical distribution that no human ever replicates. As we cover in our guide on whether LinkedIn detects randomised delays, even random timing can be flagged if the distribution itself is algorithmically generated rather than purpose-driven.
Why Cloud Tools Are Not Automatically Safer for LinkedIn Automation?
A widespread misconception in LinkedIn automation is that moving from a browser extension to a cloud-based tool eliminates detection risk. It does not.
Cloud tools that run headless Chrome on shared data-centre servers replace DOM injection risk with TLS fingerprint risk, IP reputation risk, and session geography risk simultaneously. The tool architecture changes; the detection exposure does not automatically improve. Cloud tools are genuinely safer only when they combine dedicated residential IPs, authentic browser fingerprinting, human-like behavioural execution, and activity confined to the account’s normal geographic location and working hours.
The hardest-to-detect architecture in 2026 is a hybrid model: real Chrome session on a real device and IP, with cloud logic managing pacing, sequencing, and personalisation. This produces a genuine TLS fingerprint, a real residential IP, and a fully populated browser environment that LinkedIn’s systems cannot distinguish from manual activity. Sign up to Konnector.ai free — our execution model is built around exactly this architecture.
LinkedIn Automation That Passes Every Detection Layer
Konnector.ai uses a hybrid execution model — combining controlled browser-based actions in a real LinkedIn session with cloud-orchestrated logic for pacing, personalisation, and sequencing. No headless Chrome on shared servers. No DOM injection. No data-centre IPs. Just LinkedIn automation that looks exactly like a focused professional doing intentional work.
📅 Book a Free Demo → See how Konnector.ai’s architecture handles every detection layer LinkedIn uses in 2026.
⚡ Sign Up Free → Start safe LinkedIn automation today — no headless browsers, no ban risk.
11x Your LinkedIn Outreach With
Automation and Gen AI
Harness the power of LinkedIn Automation and Gen AI to amplify your reach like never before. Engage thousands of leads weekly with AI-driven comments and targeted campaigns—all from one lead-gen powerhouse platform.
Frequently Asked Questions
LinkedIn uses multiple detection layers simultaneously, including TLS fingerprinting, the navigator.webdriver flag, missing browser properties (plugins, WebGL, window.chrome), DOM injection signals, IP tracking, and behavioural analysis. These combined signals make headless automation highly detectable.
Yes. Default Puppeteer and Playwright setups expose clear automation signals such as navigator.webdriver = true, empty plugin lists, software-rendered WebGL, and identifiable JavaScript objects. LinkedIn actively checks for these indicators in real time.
TLS fingerprinting analyses how a browser initiates a secure connection. Headless tools produce a different handshake pattern compared to real browsers, allowing LinkedIn to detect automation before the page even loads.
Yes. LinkedIn can identify mismatches in IP behaviour, TLS fingerprints, and geolocation patterns before user actions occur, making network-level detection one of the earliest filters.
No. Cloud-based tools often increase risk if they rely on data-centre IPs, shared proxies, or default browser configurations. Safety depends on combining real browser signals, residential IPs, and human-like behaviour.
The safest approach is a hybrid model using a real Chrome browser session on your actual device and IP, combined with smart automation logic for scheduling and sequencing. This produces natural, human-like signals.
Yes. Frequent IP switching, mismatched geolocations, or “impossible travel” patterns (logging in from different countries within short timeframes) are strong indicators of automation.
Impossible travel occurs when an account appears to log in from geographically distant locations within an unrealistic timeframe. LinkedIn flags this as suspicious behaviour and may restrict the account.
Yes. LinkedIn can detect DOM injections and unusual script behaviour caused by extensions. Poorly built tools leave identifiable traces in the browser environment.
Yes. LinkedIn tracks click timing, typing patterns, scrolling behaviour, and interaction sequences. Perfectly timed or repetitive actions are strong indicators of automation.
LinkedIn automation is not illegal, but it can violate LinkedIn’s terms of service if it mimics non-human behaviour or uses unauthorised tools. This can lead to warnings, restrictions, or account bans.
Yes. Personalised, human-like messaging reduces spam signals and improves engagement. While it doesn’t eliminate detection risk, it significantly improves overall campaign performance.
Residential IPs help mimic real user behaviour by aligning your activity with a consistent geographic location. They reduce suspicion compared to data-centre or shared proxy IPs.
Yes. Fixed intervals, bulk sends, or unnatural activity spikes are easily detectable. Natural variation in timing is essential to mimic human behaviour.
Yes. LinkedIn analyses deeper browser attributes such as device configuration, rendering behaviour, installed plugins, and hardware signals to build a unique browser fingerprint.
Browser fingerprinting is the process of identifying a user based on unique browser and device characteristics. Automation tools often fail to replicate these accurately, making detection easier.
Use real browser sessions, consistent IP addresses, gradual activity scaling, personalised messaging, and natural timing variations. Avoid aggressive volume and unnatural patterns.
Relying on volume over quality. High-volume, generic outreach with poor timing and no personalisation is the fastest way to trigger detection and reduce reply rates.
Yes. Logging in from multiple devices or unfamiliar environments frequently can trigger security checks and increase detection risk.
Manual outreach is inherently safer because it produces natural human signals. However, well-configured automation that mimics human behaviour can achieve similar safety levels.







